This walk-though will show us how simple it is to integrate Approov in a current API server using NodeJS and the Express framework.
We will see the requirements, dependencies and a step by step walk-through of the code necessary to implement Approov in a NodeJS Express API.Before we tackle the integration of Approov we need first to know how Approov validation is processed in the server and how to setup the environment to follow this walk-through.
Note that this article assumes a basic understanding of the Approov mechanics. If you need an overview of that, please read first the Approov in Detail page.
Approov Validation Process
Before we dive into the code we need to understand the Approov validation process on the back-end side.
The Approov Token
API calls protected by Approov will typically include a header holding an Approov JWT token. This token must be checked to ensure it has not expired and that it is properly signed with the secret shared between the back-end and the Approov cloud service.
We will use a NodeJS package to help us in the validation of the Approov JWT token.
NOTE
Just to be sure that we are on the same page, a JWT token has 3 parts which are separated by dots and represented as a string in the format of header.payload.signature. Read more about JWT tokens.
The Approov Token Binding
When an Approov token contains the key pay, its value is a base64 encoded sha256 hash of some unique identifier in the request, that we may want to bind with the Approov token, in order to enhance the security on that request, like an Authorization token.
Dummy example for the JWT token middle part, the payload:
{
"exp": 123456789, # required - the timestamp for when the token expires.
"pay":"f3U2fniBJVE04Tdecj0d6orV9qT9t52TjfHxdUqDBgY=" # optional - a sha256 hash of the token binding, encoded with base64.
}
The token binding in an Approov token is the one in the pay key:
"pay":"f3U2fniBJVE04Tdecj0d6orV9qT9t52TjfHxdUqDBgY="
ALERT: Please bear in mind that the token binding is not meant to pass application data to the API server.
System Clock
In order to correctly check for the expiration times of the Approov tokens it is very important that the Node Express server is automatically synchronizing the system clock over the network with an authoritative time source. In Linux this is usually done with an NTP server.
Requirements
The example code in this walk-through is based on the Approov Shapes API server which runs on NodeJS 10 LTS and Express 4 framework. The full source code can be found in this Github repository.
Docker is required only if you want to use the docker environment provided by the stack bash script, which is a wrapper around docker commands.
Postman is the tool we recommend to be used when simulating the queries against the API, but feel free to use any other tool of your choice.
The Docker Stack
We recommend the use of the included Docker stack to play with this Approov integration.
For details in how to use it, you need to follow the setup instructions in the Approov Shapes API Server walk-through, but feel free to use your local environment to play with this Approov integration.
The Postman Collection
As you go through your Approov Integration you may want to test it and if you are using Postman then you can import this Postman collection to see how it's done for the Approov Shapes API Server example, and use it as the base to create your own collection.
The Approov tokens used in the headers of this Postman collection where manually created with bash commands that used the dummy secret set on the .env.example file to sign all the Approov tokens.
If you are using the Aproov secret retrieved with the Approov CLI tool then you need to use it to generate some valid and invalid tokens. Some examples of using it can be found in the Approov docs.
Install Dependencies
If not already using the NPM packages express-jwt and dotenv in your project, please add them:
npm install --save express-jwt dotenv debug
Original Server
Let’s use the original-server.js as an example of a current server to which we want to add Approov to protect some or all the endpoints.
After we add only the necessary code to integrate Approov, the end result will look like we have now in the approov-protected-server.js.
How to Integrate
You will learn how to go from the original-server.js to the approov-protected-server.js and how to configure the server, but before you start this Approov integration on your own backend you may want to follow one of this simple Hello servers examples, with the Approov token check, that will give you the bases how Approov works and how it fits easily in any NodeJS Express API server, and afterwards you can come back here to follow this more advanced Approov integration.
In order to be able to check the Approov token, the express-jwt library needs to know the secret used by the Approov cloud service to sign it. A secure way to do this is by passing it as an environment variable, as you can see here.
Next you need to define two callbacks to be used during the Approov token check process. One callback is to perform the check itself with the library express-jwt and the other is to handle any errors occurred during that check.
Let’s breakdown the example implementation to make it easier to adapt to your current project.
Require Dependencies
You need to require the dependencies you installed before.
const debug = require('debug')('approov-protected-server')
Approov Protected Server file:
const { expressjwt: jwt } = require('express-jwt')
const crypto = require('crypto')
Setup Environment
If you don’t have already an .env file, then you need to create one in the root of your project by using this .env.example as your starting point.
The .env file must contain these two variables:
APPROOV_BASE64_SECRET=h+CX0tOzdAAR9l15bWAqvq7w9olk66daIH+Xk+IAHhVVHszjDzeGobzNnqyRze3lw/WVyWrc2gZfh3XXfBOmww==
APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN=true
APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN_BINDING=true
APPROOV_LOGGING_ENABLED=true
Now we can read them from our code, as is done in the configuration file:
///////////////////////////
/// APPROOV ENVIRONMENT
//////////////////////////
let isToAbortRequestOnInvalidToken = true
let isToAbortOnInvalidBinding = true
let isApproovLoggingEnabled = true
const abortRequestOnInvalidToken = dotenv.parsed.APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN || 'true'
const abortOnInvalidTokenBinding = dotenv.parsed.APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN_BINDING || 'true'
const approovLoggingEnabled = dotenv.parsed.APPROOV_LOGGING_ENABLED || 'true'
if (abortRequestOnInvalidToken.toLowerCase() === 'false') {
isToAbortRequestOnInvalidToken = false
}
if (abortOnInvalidTokenBinding.toLowerCase() === 'false') {
isToAbortOnInvalidBinding = false
}
if (approovLoggingEnabled.toLowerCase() === 'false') {
isApproovLoggingEnabled = false
}
const approov = {
abortRequestOnInvalidToken: isToAbortRequestOnInvalidToken,
abortRequestOnInvalidTokenBinding: isToAbortOnInvalidBinding,
approovLoggingEnabled: isApproovLoggingEnabled,
// The Approov base64 secret must be retrieved with the Approov CLI tool
base64Secret: dotenv.parsed.APPROOV_BASE64_SECRET,
}
////////////////////////////
/// EXPORT CONFIGURATION
///////////////////////////
module.exports = {
server,
approov,
}
Customizable Approov Callbacks
These are callbacks used in the Approov Integration that you may want to customize to the needs of your application.
Let’s start with the logging callback that we can see in approov-protected-server.js:
// Callback to be customized with your preferred way of logging.
const logApproov = function(req, res, message) {
debug(buildLogMessagePrefix(req, res) + ' ' + message)
}
Next we have the callback to get the token binding value that we want to compare against the value of the key pay in the Approov token, as seen in approov-protected-server.js:
// Callback to be personalized in order to get the token binding header value being used by
// your application.
// In the current scenario we use an Authorization token, but feel free to use what
// suits best your needs.
const getTokenBindingHeader = function(req) {
return req.get('Authorization')
}
Each time an Approov token doesn’t validate for any reason, the Approov integration will pass the control to the application logic by invoking a callback such as the one defined in approov-protected-server.js:
// Callback to be customized with how you want to handle a request with an
// invalid Approov token.
// The code included in this callback is provided as an example, that you can
// keep or totally change it in a way that best suits your needs.
const handlesRequestWithInvalidApproovToken = function(err, req, res, next, httpStatusCode) {
logApproov(req, res, 'APPROOV TOKEN: ' + err)
// Logging a message to make clear in the logs what was the action we took.
// Feel free to skip it if you think is not necessary to your use case.
let message = 'REQUEST WITH INVALID APPROOV TOKEN'
if (config.approov.abortRequestOnInvalidToken === true) {
buildBadRequestResponse(req, res, httpStatusCode, 'REJECTED ' + message)
return
}
message = 'ACCEPTED ' + message
logApproov(req, res, message)
next()
return
}
The last customizable callback will be invoked by the Approov integration to allow the application to decide what action to take when the Approov token binding is invalid, as defined in approov-protected-server.js:
// Callback to be customized with how you want to handle a request where the
// token binding in the request header doesn't match the the one in the Approov token.
// The code included in this callback is provided as an example, that you can
// keep or totally change it in a way that best suits your needs.
const handlesRequestWithInvalidTokenBinding = function(req, res, next, httpStatusCode, message) {
logApproov(req, res, message)
// Logging here to make clear in the logs what was the action we took.
// Feel free to skip it if you think is not necessary to your use case.
let logMessage = 'REQUEST WITH INVALID APPROOV TOKEN BINDING'
if (config.approov.abortRequestOnInvalidTokenBinding === true) {
buildBadRequestResponse(req, res, httpStatusCode, 'REJECTED ' + logMessage)
return
}
logApproov(req, res, 'ACCEPTED ' + logMessage)
next()
return
}
Approov Integration Core Callbacks
These core callbacks are specific to the Approov integration, and since they don’t interfere with the flow or behavior of your application, we think they are not in need of being customized.
Helper Functions
The core callbacks will need some very basic helper functions, like the ones defined in the approov-protected-server:
const isEmpty = function(value) {
return (value === undefined) || (value === null) || (value === '')
}
const isString = function(value) {
return (typeof(value) === 'string')
}
const isEmptyString = function(value) {
return (isEmpty(value) === true) || (isString(value) === false) || (value.trim() === '')
}
Approov Token
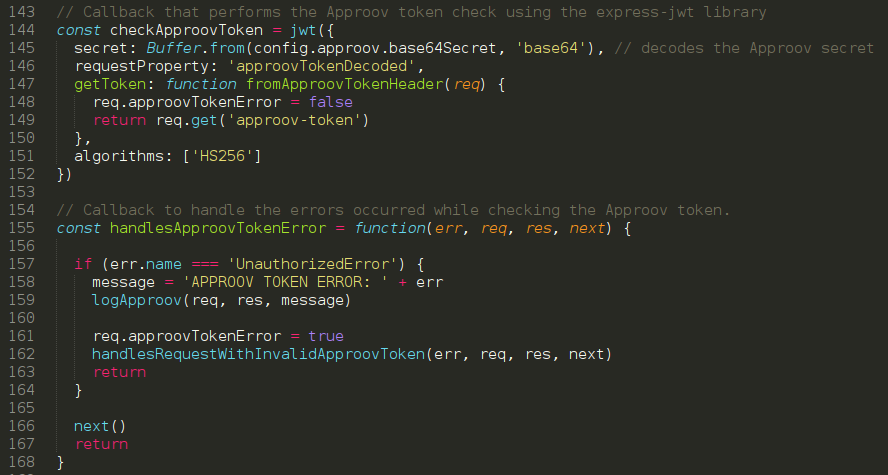
This callback will be used in the middleware to check the Approov token:
// Callback that performs the Approov token check using the express-jwt library
const checkApproovToken = jwt({
secret: Buffer.from(config.approov.base64Secret, 'base64'), // decodes the Approov secret
requestProperty: 'approovTokenDecoded',
getToken: function fromApproovTokenHeader(req, res) {
req.approovTokenError = false
const approovToken = req.get('Approov-Token')
if (isEmptyString(approovToken)) {
req.approovTokenError = true
throw new Error('token empty or missing in the header of the request.')
}
return approovToken
},
algorithms: ['HS256']
})
Then we need this callback to handle any error that may occur during the Approov token check:
// Callback to handle the errors occurred while checking the Approov token.
const handlesApproovTokenError = function(err, req, res, next) {
if (req.approovTokenError === true) {
// When we reach here, it means the header `Approov-Token` is empty or is missing.
// @see checkApproovToken()
handlesRequestWithInvalidApproovToken(err, req, res, next, 400)
return
}
if (err.name === 'UnauthorizedError') {
// When we reach here, it means that an Error was thrown by the express-jwt
// library while decoding the Approov token.
// @see checkApproovToken()
req.approovTokenError = true
handlesRequestWithInvalidApproovToken(err, req, res, next, 401)
return
}
next()
return
}
Finally we want to handle when the Approov token succeeds in the validation process, as we have done approov-protected-server.js
// Callback to handles when an Approov token is successfully validated.
const handlesApproovTokenSuccess = function(req, res, next) {
if (req.approovTokenError === false) {
logApproov(req, res, 'ACCEPTED REQUEST WITH VALID APPROOV TOKEN')
}
next()
return
}
Approov Token Binding
We will use this function to validate if the token binding value in the request matches the token binding value in the Approov token, as we can see in the approov-protected-server.js:
// Callback to check the Approov token binding in the header matches with the one in the key `pay` of the Approov token claims.
const handlesApproovTokenBindingVerification = function(req, res, next){
if (req.approovTokenError === true) {
next()
return
}
// The decoded Approov token was added to the request object when the checked it at `checkApproovToken()`
token_binding_payload = req.approovTokenDecoded.pay
if (token_binding_payload === undefined) {
handlesRequestWithInvalidTokenBinding(req, res, next, 400, "APPROOV TOKEN BINDING ERROR: key 'pay' is missing in the claims of the Approov token payload.")
return
}
if (isEmptyString(token_binding_payload)) {
handlesRequestWithInvalidTokenBinding(req, res, next, 400, "APPROOV TOKEN BINDING ERROR: key 'pay' in the decoded token is empty.")
return
}
// We use here the Authorization token, but feel free to use another header, but you need to bind this header to
// the Approov token in the mobile app.
const token_binding_header = getTokenBindingHeader(req)
if (isEmptyString(token_binding_header)) {
handlesRequestWithInvalidTokenBinding(req, res, next, 400, "APPROOV TOKEN BINDING ERROR: Missing or empty header to perform the verification for the token binding.")
return
}
// We need to hash and base64 encode the token binding header, because that's how it was included in the Approov
// token on the mobile app.
const token_binding_header_encoded = crypto.createHash('sha256').update(token_binding_header, 'utf-8').digest('base64')
if (token_binding_payload !== token_binding_header_encoded) {
handlesRequestWithInvalidTokenBinding(req, res, next, 401, "APPROOV TOKEN BINDING ERROR: token binding in header doesn't match with the key 'pay' in the decoded token.")
return
}
logApproov(req, res, 'ACCEPTED REQUEST WITH VALID APPROOV TOKEN BINDING')
// Let the request continue as usual.
next()
return
}
/////// THE APPROOV INTERCEPTORS ///////
Middleware
We will use the middleware approach to intercept all endpoints we want to protect with an Approov Token, so any interceptor must be placed before we declare the endpoints we want to protect, as is done in the approov-protected-server.js.
The following examples will use the callbacks we already have defined here to pass as the second parameter to the middleware interceptors.
For specific endpoints
To protect specific endpoints in a current server we only need to add the Approov interceptors for each endpoint we want to protect, as we have done here:
// Intercepts all calls to the shapes endpoint to validate the Approov token.
app.use('/v2/shapes', checkApproovToken)
// Handles failure in validating the Approov token
app.use('/v2/shapes', handlesApproovTokenError)
// Handles requests where the Approov token is a valid one.
app.use('/v2/shapes', handlesApproovTokenSuccess)
// Intercepts all calls to the forms endpoint to validate the Approov token.
app.use('/v2/forms', checkApproovToken)
// Handles failure in validating the Approov token
app.use('/v2/forms', handlesApproovTokenError)
// Handles requests where the Approov token is a valid one.
app.use('/v2/forms', handlesApproovTokenSuccess)
// Checks if the Approov token binding is valid and aborts the request when the environment variable
// APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN_BINDING is set to true in the environment file.
app.use('/v2/forms', handlesApproovTokenBindingVerification)
For all endpoints
To protect all endpoints we only need to declare the Approov interceptor for the API root endpoint / or /v2, thus we need to modify the above code to look like this:
| // file: approov-protected-server.js |
| // Intercepts all calls to the shapes endpoint to validate the Approov token. |
| app.use('/v2', checkApproovToken) |
| // Handles failure in validating the Approov token |
| app.use('/v2', handlesApproovTokenError) |
| // Handles requests where the Approov token is a valid one. |
| app.use('/v2', handlesApproovTokenSuccess) |
| // Checks if the Approov token binding is valid and aborts the request when the environment variable |
| // APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN_BINDING is set to true in the environment file. |
| app.use('/v2', handlesApproovTokenBindingVerification) |
Approov in Action
Let's see how to query the NodeJS Express API from Postman with the collection we told you to install in the requirements section.
NOTE:
For your convenience the Postman collection includes a token that only expires in the very distant future for this call "Approov Token with valid signature and expiry time". For the call "Expired Approov Token with valid signature" an expired token is also included.
Postman view with an Approov token correctly signed and not expired:

Postman view with token correctly signed but this time it is expired:

Shell view with the logs for the above requests:

Request Overview:
We used a helper script to generate an Approov Token that was valid for 1 minute.
In Postman we performed 2 requests with the same token and the first one was successful, but the second request, performed 2 minutes later, failed with a 401 response because the token had already expired as we can see by the log messages in the shell view.
Play Time for the Approov Shapes API Server
If you have not done it already, now is the time to follow the Approov Shapes API Server walk-through to get a feel for how all this works.
The Approov Shapes API Server contains endpoints with and without the Approov protection. The protected endpoints differ in the sense that one uses the optional token binding in the Approov token.
We will demonstrate how to call each API endpoint with screen-shots from Postman and from the shell. Postman is used here as an easy way to demonstrate how you can play with the Approov integration in the API server, but to see a real demo of how Approov would work in production, you need to request a demo here.
The Code Difference
If we compare the original-server.js with the approov-protected-server.js we will see this file difference:
| --- /home/sublime/workspace/node/express/server/original-server.js |
| +++ /home/sublime/workspace/node/express/server/approov-protected-server.js |
| @@ -1,4 +1,6 @@ |
| -const debug = require('debug')('original-server') |
| +const debug = require('debug')('approov-protected-server') |
| +const jwt = require('express-jwt') |
| +const crypto = require('crypto') |
| const config = require('./configuration') |
| const https = require('https') |
| const fs = require('fs') |
| @@ -60,6 +62,243 @@ |
| } |
| +//////////////////////////////////////////////////////////////////////////////// |
| +/// YOUR APPLICATION CUSTOMIZABLE CALLBACKS FOR THE APPROOV INTEGRATION |
| +//////////////////////////////////////////////////////////////////////////////// |
| +/// |
| +/// Feel free to customize this callbacks to best suite the needs your needs. |
| +/// |
| + |
| +// Callback to be customized with your preferred way of logging. |
| +const logApproov = function(req, res, message) { |
| + debug(buildLogMessagePrefix(req, res) + ' ' + message) |
| +} |
| + |
| +// Callback to be personalized in order to get the token binding header value being used by |
| +// your application. |
| +// In the current scenario we use an Authorization token, but feel free to use what |
| +// suits best your needs. |
| +const getTokenBindingHeader = function(req) { |
| + return req.get('Authorization') |
| +} |
| + |
| +// Callback to be customized with how you want to handle a request with an |
| +// invalid Approov token. |
| +// The code included in this callback is provided as an example, that you can |
| +// keep or totally change it in a way that best suits your needs. |
| +const handlesRequestWithInvalidApproovToken = function(err, req, res, next, httpStatusCode) { |
| + |
| + logApproov(req, res, 'APPROOV TOKEN: ' + err) |
| + |
| + // Logging a message to make clear in the logs what was the action we took. |
| + // Feel free to skip it if you think is not necessary to your use case. |
| + let message = 'REQUEST WITH INVALID APPROOV TOKEN' |
| + |
| + if (config.approov.abortRequestOnInvalidToken === true) { |
| + buildBadRequestResponse(req, res, httpStatusCode, 'REJECTED ' + message) |
| + return |
| + } |
| + |
| + message = 'ACCEPTED ' + message |
| + logApproov(req, res, message) |
| + next() |
| + return |
| +} |
| + |
| +// Callback to be customized with how you want to handle a request where the |
| +// token binding in the request header doesn't match the the one in the Approov token. |
| +// The code included in this callback is provided as an example, that you can |
| +// keep or totally change it in a way that best suits your needs. |
| +const handlesRequestWithInvalidTokenBinding = function(req, res, next, httpStatusCode, message) { |
| + |
| + logApproov(req, res, message) |
| + |
| + // Logging here to make clear in the logs what was the action we took. |
| + // Feel free to skip it if you think is not necessary to your use case. |
| + let logMessage = 'REQUEST WITH INVALID APPROOV TOKEN BINDING' |
| + |
| + if (config.approov.abortRequestOnInvalidTokenBinding === true) { |
| + buildBadRequestResponse(req, res, httpStatusCode, 'REJECTED ' + logMessage) |
| + return |
| + } |
| + |
| + logApproov(req, res, 'ACCEPTED ' + logMessage) |
| + next() |
| + return |
| +} |
| + |
| +// Callback to build the response when a request fails to pass the Approov checks. |
| +const buildBadRequestResponse = function(req, res, httpStatusCode, logMessage) { |
| + res.status(httpStatusCode) |
| + logApproov(req, res, logMessage) |
| + res.json({}) |
| +} |
| + |
| + |
| +//////////////////////////////////////////////////////////////////////////////// |
| +/// STARTS NON CUSTOMIZABLE LOGIC FOR THE APPROOV INTEGRATION |
| +//////////////////////////////////////////////////////////////////////////////// |
| +/// |
| +/// This section contains code that is specific to the Approov integration, |
| +/// thus we think that is not necessary to customize it, once is not |
| +/// interfering with your application logic or behavior. |
| +/// |
| + |
| +////// APPROOV HELPER FUNCTIONS ////// |
| + |
| +const isEmpty = function(value) { |
| + return (value === undefined) || (value === null) || (value === '') |
| +} |
| + |
| +const isString = function(value) { |
| + return (typeof(value) === 'string') |
| +} |
| + |
| +const isEmptyString = function(value) { |
| + return (isEmpty(value) === true) || (isString(value) === false) || (value.trim() === '') |
| +} |
| + |
| + |
| +////// APPROOV TOKEN ////// |
| + |
| + |
| +// Callback that performs the Approov token check using the express-jwt library |
| +const checkApproovToken = jwt({ |
| + secret: Buffer.from(config.approov.base64Secret, 'base64'), // decodes the Approov secret |
| + requestProperty: 'approovTokenDecoded', |
| + getToken: function fromApproovTokenHeader(req, res) { |
| + req.approovTokenError = false |
| + const approovToken = req.get('Approov-Token') |
| + |
| + if (isEmptyString(approovToken)) { |
| + req.approovTokenError = true |
| + throw new Error('token empty or missing in the header of the request.') |
| + } |
| + |
| + return approovToken |
| + }, |
| + algorithms: ['HS256'] |
| +}) |
| + |
| +// Callback to handle the errors occurred while checking the Approov token. |
| +const handlesApproovTokenError = function(err, req, res, next) { |
| + |
| + if (req.approovTokenError === true) { |
| + // When we reach here, it means the header `Approov-Token` is empty or is missing. |
| + // @see checkApproovToken() |
| + handlesRequestWithInvalidApproovToken(err, req, res, next, 400) |
| + return |
| + } |
| + |
| + if (err.name === 'UnauthorizedError') { |
| + // When we reach here, it means that an Error was thrown by the express-jwt |
| + // library while decoding the Approov token. |
| + // @see checkApproovToken() |
| + req.approovTokenError = true |
| + handlesRequestWithInvalidApproovToken(err, req, res, next, 401) |
| + return |
| + } |
| + |
| + next() |
| + return |
| +} |
| + |
| +// Callback to handles when an Approov token is successfully validated. |
| +const handlesApproovTokenSuccess = function(req, res, next) { |
| + |
| + if (req.approovTokenError === false) { |
| + logApproov(req, res, 'ACCEPTED REQUEST WITH VALID APPROOV TOKEN') |
| + } |
| + |
| + next() |
| + return |
| +} |
| + |
| + |
| +////// APPROOV TOKEN BINDING ////// |
| + |
| + |
| +// Callback to check the Approov token binding in the header matches with the one in the key `pay` of the Approov token claims. |
| +const handlesApproovTokenBindingVerification = function(req, res, next){ |
| + |
| + if (req.approovTokenError === true) { |
| + next() |
| + return |
| + } |
| + |
| + // The decoded Approov token was added to the request object when the checked it at `checkApproovToken()` |
| + token_binding_payload = req.approovTokenDecoded.pay |
| + |
| + if (token_binding_payload === undefined) { |
| + logApproov(req, res, "APPROOV TOKEN BINDING WARNING: key 'pay' is missing.") |
| + logApproov(req, res, 'ACCEPTED REQUEST WITH APPROOV TOKEN BINDING MISSING') |
| + next() |
| + return |
| + } |
| + |
| + if (isEmptyString(token_binding_payload)) { |
| + handlesRequestWithInvalidTokenBinding(req, res, next, 400, "APPROOV TOKEN BINDING ERROR: key 'pay' in the decoded token is empty.") |
| + return |
| + } |
| + |
| + // We use here the Authorization token, but feel free to use another header, but you need to bind this header to |
| + // the Approov token in the mobile app. |
| + const token_binding_header = getTokenBindingHeader(req) |
| + |
| + if (isEmptyString(token_binding_header)) { |
| + handlesRequestWithInvalidTokenBinding(req, res, next, 400, "APPROOV TOKEN BINDING ERROR: Missing or empty header to perform the verification for the token binding.") |
| + return |
| + } |
| + |
| + // We need to hash and base64 encode the token binding header, because that's how it was included in the Approov |
| + // token on the mobile app. |
| + const token_binding_header_encoded = crypto.createHash('sha256').update(token_binding_header, 'utf-8').digest('base64') |
| + |
| + if (token_binding_payload !== token_binding_header_encoded) { |
| + handlesRequestWithInvalidTokenBinding(req, res, next, 401, "APPROOV TOKEN BINDING ERROR: token binding in header doesn't match with the key 'pay' in the decoded token.") |
| + return |
| + } |
| + |
| + logApproov(req, res, 'ACCEPTED REQUEST WITH VALID APPROOV TOKEN BINDING') |
| + |
| + // Let the request continue as usual. |
| + next() |
| + return |
| +} |
| + |
| +/////// THE APPROOV INTERCEPTORS /////// |
| + |
| +// Intercepts all calls to the shapes endpoint to validate the Approov token. |
| +app.use('/v2/shapes', checkApproovToken) |
| + |
| +// Handles failure in validating the Approov token |
| +app.use('/v2/shapes', handlesApproovTokenError) |
| + |
| +// Handles requests where the Approov token is a valid one. |
| +app.use('/v2/shapes', handlesApproovTokenSuccess) |
| + |
| +// Intercepts all calls to the forms endpoint to validate the Approov token. |
| +app.use('/v2/forms', checkApproovToken) |
| + |
| +// Handles failure in validating the Approov token |
| +app.use('/v2/forms', handlesApproovTokenError) |
| + |
| +// Handles requests where the Approov token is a valid one. |
| +app.use('/v2/forms', handlesApproovTokenSuccess) |
| + |
| +// Checks if the Approov token binding is valid and aborts the request when the environment variable |
| +// APPROOV_ABORT_REQUEST_ON_INVALID_TOKEN_BINDING is set to true in the environment file. |
| +app.use('/v2/forms', handlesApproovTokenBindingVerification) |
| + |
| +/// NOTE: |
| +/// Is important to place all the Approov interceptors before we declare the |
| +/// endpoints of the API, otherwise they will not be able to intercept any |
| +/// request. |
| + |
| +//////////////////////////////////////////////////////////////////////////////// |
| +/// ENDS APPOOV INTEGRATION |
| +//////////////////////////////////////////////////////////////////////////////// |
| + |
| //////////////// |
| // ENDPOINTS |
| //////////////// |
| @@ -84,6 +323,28 @@ |
| app.get('/v1/forms', function(req, res, next) { |
| logResponseToRequest(req, res) |
| buildFormsResponse(res, 'unprotected') |
| +}) |
| + |
| +/** |
| + * V2 ENDPOINTS |
| + */ |
| + |
| +// simple 'hello world' endpoint. |
| +app.get('/v2/hello', function (req, res, next) { |
| + logResponseToRequest(req, res) |
| + buildHelloWorldResponse(res) |
| +}) |
| + |
| +// shapes endpoint returns a random shape. |
| +app.get('/v2/shapes', function(req, res, next) { |
| + logResponseToRequest(req, res) |
| + buildShapesResponse(res, 'protected') |
| +}) |
| + |
| +// shapes endpoint returns a random form. |
| +app.get('/v2/forms', function(req, res, next) { |
| + logResponseToRequest(req, res) |
| + buildFormsResponse(res, 'protected') |
| }) |
As we can see the Approov integration in the current server is simple, easy and is done with just a few lines of code.
If you have not done it already, now is time to follow the Approov Shapes API Server walk-through to understand the flow.
Production
In order to protect the communication between your mobile app and the API server is important to only communicate over a secure communication channel, also known as https.
Please bear in mind that https on its own is not enough, certificate pinning must be also used to pin the connection between the mobile app and the API server in order to prevent Man-in-the-Middle Attacks.
We do not use https and certificate pinning in this Approov integration example because we want to be able to run the Approov Shapes API Server in localhost.
However in production is mandatory to implement and configure certificate pinning, that is made easy by using the dynamic pinning feature built-in the Appoov CLI tool, that allows to update the pins without the need to release a new version of your mobile app.

Paulo Renato
Paulo Renato is known more often than not as paranoid about security. He strongly believes that all software should be secure by default. He thinks security should be always opt-out instead of opt-in and be treated as a first class citizen in the software development cycle, instead of an after thought when the product is about to be finished or released.