What is the difference between 'Device Attestation' and 'App Attestation'?
Decoding Mobile App Security: Device Attestation vs. App Attestation
Introduction: In the expanding cybersecurity landscape, mobile app security has become paramount as users increasingly rely on these powerful devices. Two integral security components, 'device attestation' and 'app attestation', play distinct yet interconnected roles in fortifying the security of mobile applications. This KB post unravels the nuances of device attestation and app attestation, comparing and contrasting their contributions to mobile app security while addressing notable threats specific to each.
Device Attestation: Device attestation focuses on verifying the integrity and security of the entire mobile device including the hardware, firmware and software including the OS. This process involves confirming that a mobile device is free from compromise and adheres to predefined security standards. Notable threats that device attestation seeks to address include the risk of rooted devices, amongst other threats. Device attestation can also be called: 'device integrity checks' or 'app shielding'.
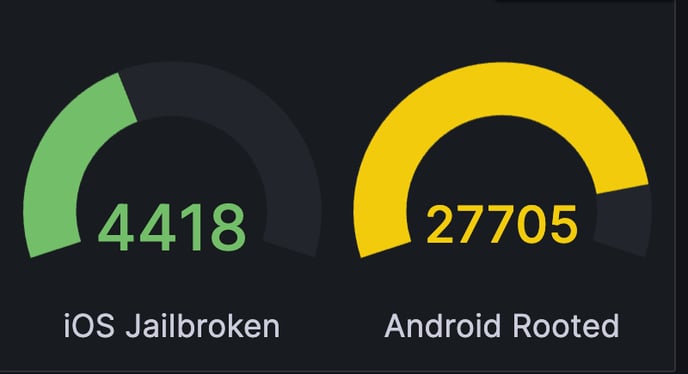
Rooted or jailbroken devices pose a significant security concern as they bypass built-in security measures, potentially exposing the entire device to vulnerabilities and unauthorized access.
App Attestation: On the other hand, app attestation hones in on the security of individual mobile applications. It involves validating the integrity of an app's runtime environment, ensuring that it hasn't been compromised or manipulated. This can include the detection of debuggers, hooking frameworks, Cydia, Magisk, Frida, Riru and other pervasive threats like GameGuardian. Notable threats associated with app attestation include the danger of modified or repackaged apps. Hackers may attempt to alter the code or behavior of an application, introducing malicious elements that can compromise user data or disrupt the normal functioning of the app or associated APIs.
Comparisons:
-
Scope of Security:
- Device attestation secures the entire device, providing a comprehensive layer of protection against threats like rooted or jailbroken devices.
- App attestation, while more focused, safeguards individual applications against specific threats, such as modified apps.
-
Verification Targets:
- Device attestation verifies the overall security state of the device, including hardware and firmware, to mitigate risks associated with rooted devices.
- App attestation specifically targets the runtime environment and code integrity of a particular mobile application, countering threats related to modified apps.
-
Use Cases:
- Device attestation is essential for scenarios where the overall device security is paramount, especially in environments where rooted devices may pose a risk.
- App attestation is crucial for protecting individual applications, particularly in sectors like finance or healthcare, where the threat of modified apps can compromise data integrity.
Contrasts:
-
Granularity of Protection:
- Device attestation provides a broader scope of protection against threats like rooted devices but may not catch threats specific to individual applications.
- App attestation offers a more granular approach, securing applications against threats like modified apps that might not impact the entire device.
-
Resource Utilization:
- Device attestation, involving comprehensive checks against rooted devices, may consume more system resources.
- App attestation, focusing on specific applications, can be more resource-efficient, particularly when mitigating risks related to modified apps.
 Conclusion: In navigating mobile app security, understanding the distinctions between device attestation and app attestation is important. While device attestation safeguards the holistic device environment, app attestation provides targeted protection for individual applications. Both play indispensable roles in creating a robust defense against the evolving landscape of mobile security, addressing threats such as rooted devices and modified apps. The choice between device attestation and app attestation depends on the specific security requirements and use cases of the mobile ecosystem in question.
Conclusion: In navigating mobile app security, understanding the distinctions between device attestation and app attestation is important. While device attestation safeguards the holistic device environment, app attestation provides targeted protection for individual applications. Both play indispensable roles in creating a robust defense against the evolving landscape of mobile security, addressing threats such as rooted devices and modified apps. The choice between device attestation and app attestation depends on the specific security requirements and use cases of the mobile ecosystem in question.